Sixteen months after open source, MCP no longer asks for a seat at the integration table — it has rewired what the table is for.
From tool-calling shim to enterprise middleware: a 16-month evolution
Anthropic open-sourced the Model Context Protocol in November 2024 with a deliberately modest framing: a standard for connecting AI assistants to tools and data sources, designed to replace one-off integrations with a shared protocol. Sixteen months later, that framing understates what shipped. By April 2026 the protocol records 97 million monthly SDK downloads, 10,000-plus published MCP servers, native support across Claude, ChatGPT, Gemini, and Microsoft Copilot, and a Gartner forecast that 75 percent of API gateway vendors will include MCP support by 2026. Anthropic donated the protocol to the Linux Foundation’s Agentic AI Foundation in December 2025; the foundation now lists 146 members across three tiers, with platinum sponsors including AWS, Anthropic, Block, Bloomberg, Cloudflare, Google, Microsoft, and OpenAI.
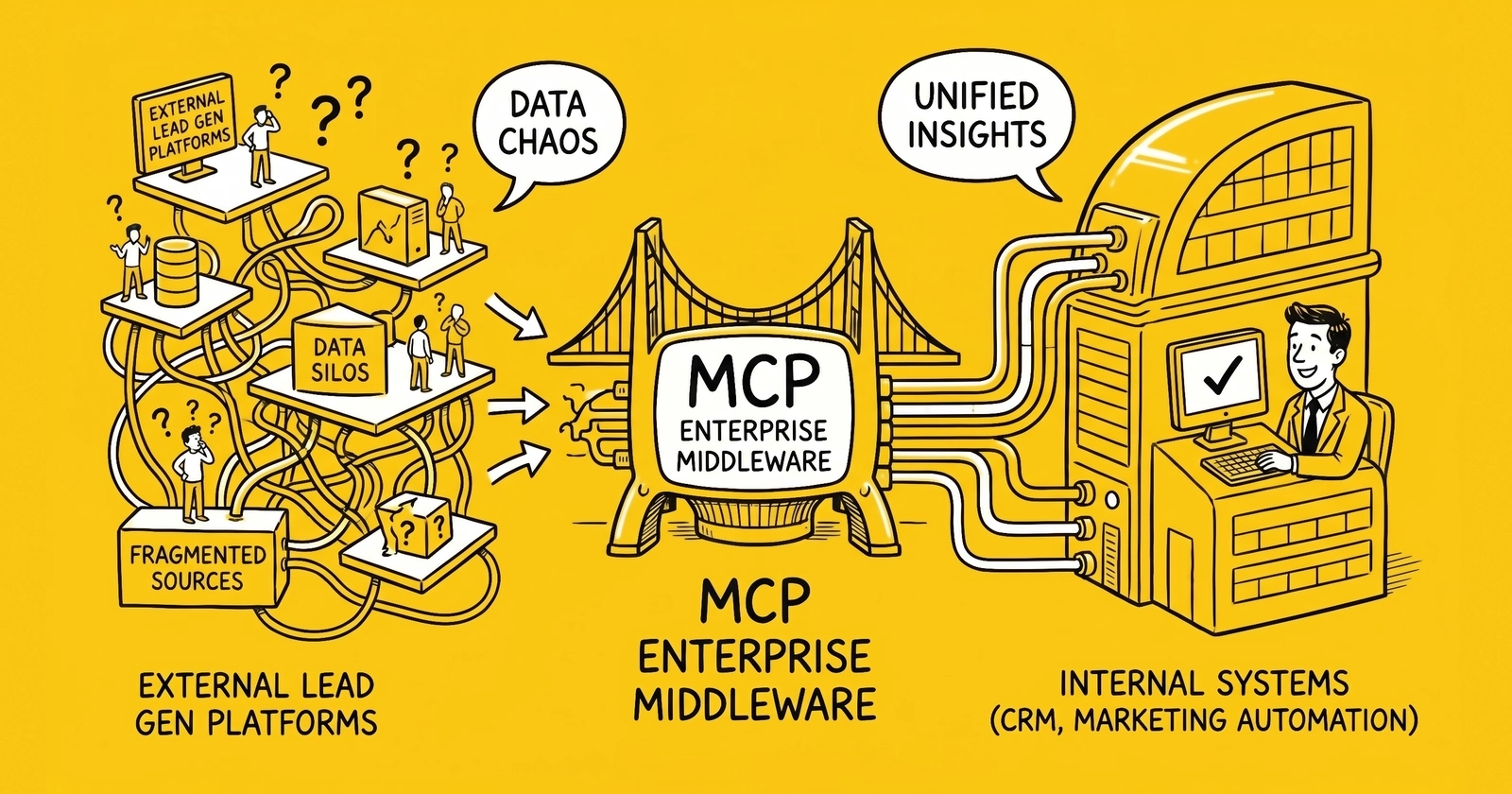
The interesting story is not the adoption velocity. It is the architectural reclassification. Operators who treated MCP as a translation layer in 2025 — a way to wrap existing APIs so an LLM could call them — now find themselves shipping production deployments that look unmistakably like middleware. Cloudflare wraps 2,500 endpoints across DNS, Workers, R2, D1, and Zero Trust through a single MCP server using a “Code Mode” pattern that consumes roughly 1,000 tokens versus the 1.17 million tokens required if every endpoint were exposed individually. Block runs 60-plus internal MCP servers across 12,000 employees in 15-plus job functions, with engineers reporting up to 75 percent reduction in time spent on daily engineering tasks. Salesforce ships hosted MCP servers for CRM data, a developer-experience server with 60-plus tools, and a MuleSoft MCP Connector that bridges any connected legacy system — SAP, Oracle, mainframe SOAP services — to AI agents.
The distinction between a protocol shim and middleware matters for lead-generation operators because the architectural commitments differ. A translation layer is something a vendor adds; middleware is something an organization builds infrastructure around. When Phonexa or boberdoo or LeadsPedia decides whether to expose its routing logic as MCP-accessible tools, the question is not “should we add an AI integration.” It is whether to ship an AI-native semantic interface that competing platforms will commodify within 18 months if it is not shipped first. The same logic that drove ping-post adoption in 2008 — buyers wanted real-time auctions, sellers who refused saw lower fill rates — now applies to MCP-compatible inventory. AI procurement agents prefer suppliers with semantic tool definitions over those exposing only REST endpoints.
The protocol’s three-primitive design clarifies why this transition happened faster than analysts expected.
The three primitives — tools, resources, prompts
The most common misconception about MCP is that it simply wraps API endpoints for LLM function-calling. The protocol actually defines three core server primitives — tools, resources, and prompts — each serving a different actor in the AI application stack. Tools are model-controlled executable functions. Resources are application-controlled data sources identified by URIs with metadata including human-readable names, descriptions, MIME types, and size information. Prompts are user-controlled reusable templates that structure interactions.
This tripartite design means an MCP server is not a thin translation layer but a semantic product interface. Every tool definition carries a machine-readable name, a human-readable title, a natural-language description, typed JSON Schema for inputs and outputs, and behavioral annotations. When an agent calls tools/list, it receives not just endpoint signatures but business context — what a capability does, when to use it, and what constraints apply. Itential’s engineering team frames the implication directly: “MCP becomes a semantic contract, not a mechanical one. The model shouldn’t have to assemble an outcome from ten raw endpoints if your automation platform already understands the domain logic.”
The dynamic discovery mechanism is the architectural break from traditional middleware. Via tools/list, resources/list, and prompts/list, AI agents discover available capabilities at runtime without pre-configuration. When capabilities change, servers emit notifications/tools/list_changed events. Traditional ESBs, API gateways, and iPaaS platforms require design-time registration through WSDL, OpenAPI specs, or adapter configuration. MCP flips this model: agents ask “What can you do?” and negotiate capabilities during initialization. This is what makes it middleware, not merely a protocol.
For a lead-distribution platform, the implication is concrete. A REST endpoint exposing /leads/route requires a buyer’s developer team to read documentation, write a client, and ship code. The same capability exposed as an MCP tool with the description “Route a lead to the highest-bidding buyer in the auction waterfall, returning buyer ID, price paid, and TCPA disposition” lets a buyer’s procurement agent discover and invoke routing logic in one cycle. Multiplied across 47 platforms in the lead-distribution space, the discoverability gap becomes a competitive moat for early movers.
How the primitives map to lead-gen capability surfaces
The mapping between MCP primitives and lead-gen platform capabilities is not abstract. It corresponds to specific surfaces operators already expose through proprietary APIs.
| MCP Primitive | Controlled by | Lead-gen example | Replaces today |
|---|---|---|---|
| Tool | LLM/agent | route_lead, validate_consent, query_buyer_sla, score_lead | Documented REST endpoint with bespoke client |
| Resource | Application | Buyer-rules document, vertical configuration, DNC scrub list, TrustedForm certificate | Static config files, manual API calls |
| Prompt | User | ”Onboard a new auto-insurance buyer with 60-day return SLA” template | Tribal knowledge, runbooks, support tickets |
The third row is where most operators underinvest. Prompts as a primitive let a platform encode standard operating procedures — onboarding, dispute resolution, SLA negotiation — as reusable templates an agent can invoke on behalf of a buyer or seller. boberdoo’s onboarding wizard, Phonexa’s campaign-launch flow, and LeadsPedia’s affiliate-approval workflow could all surface as MCP prompts long before any platform exposes write-access tools.
The agentic semantic layer in production
The concept of an agentic semantic layer — a metadata layer between AI agents and enterprise data that defines business metrics, enforces access control, and exposes governed query interfaces — has moved from whiteboard architecture to production deployment. At least ten companies now ship MCP servers that expose governed business semantics rather than raw data.
dbt exposes its Semantic Layer through MCP, letting agents query governed metric definitions, explore metadata, and view lineage without generating raw SQL. AtScale ships a containerized MCP server where, as founder Dave Mariani describes it, “the semantic layer defines ‘what’ the data means; MCP defines ‘how’ that meaning is shared with AI tools.” Dremio built one of the first enterprise-grade MCP servers atop its Unified Semantic Layer, with agents invoking tools like Run SQL Query and Run Semantic Search against curated datasets with field-level meaning and role-based access controls. Looker on Google Cloud ensures AI agents “directly query a single source of truth” of governed business metrics. Strategy — formerly MicroStrategy — powers its agents through a Universal Semantic Layer with row-level access control. A retail branch manager asking Gemini about sales triggers MCP authentication, permission validation, authorized data retrieval, and contextual insight generation in a single governed flow.
Bonnard, a startup building an explicitly “agent-native” semantic layer, crystallizes the distinction: “The agent calls explore_schema to see what metrics exist, then query to fetch data. It never generates SQL. It never interprets column names. It queries governed definitions.” Metrics are defined in YAML, exposed via MCP, with multi-tenancy enforced structurally rather than through prompt engineering. TimeXtender articulates the gap this fills: “MCP solves the N×M integration challenge while leaving an even more fundamental gap — AI agents lack the business context necessary to understand what your data means.” Their MCP server exposes not just column names but business glossaries, data lineage, quality scores, and ownership.
For lead-gen operators, the agentic semantic layer is the missing piece in conversations about agentic commerce. Articles on agentic commerce and AI agents in lead generation typically focus on the buyer-side agent — the one issuing purchase queries. The seller-side equivalent is the semantic layer: a governed surface where metrics like cost per lead, conversion-to-buyer rate, return rate, and TCPA-compliance percentage are exposed with definitions an agent does not need to reverse-engineer. A lead-distribution platform that exposes “fill rate” as a raw column in a database forces every buyer agent to learn that platform’s semantics. The same metric exposed through an MCP semantic layer with the definition “Percentage of inbound leads matched to a buyer in the auction waterfall within SLA, computed across rolling 7-day windows excluding test traffic” is portable across buyers and durable across platform schema changes.
This pattern — semantic metadata layered on top of MCP’s transport — transforms the protocol from a connector into an enterprise knowledge interface.
MCP vs ESB, API gateway, and iPaaS
MCP operates at a fundamentally different layer than traditional enterprise middleware, but the comparison reveals both its unique strengths and significant gaps. Operators evaluating MCP adoption need a clear picture of what it does and does not replace.
Against ESBs (MuleSoft ESB, IBM Integration Bus): ESBs are built for human-designed, deterministic workflows between applications — content-based routing, message splitting, XA transactions, guaranteed delivery. MCP replaces none of this. It introduces AI-driven, non-deterministic orchestration where the LLM decides the workflow at runtime. An ESB routes messages between predetermined endpoints based on rules configured by humans. An MCP server lets an agent reason about which tools to invoke, in what sequence, with what parameters, based on user intent. They solve different problems at different layers.
Against API gateways (Kong, Apigee, AWS API Gateway): API gateways handle stateless north-south traffic — external clients to internal services — at the perimeter using URL path matching and header-based routing. MCP handles stateful east-west traffic — agent to tool — inside the enterprise. MCP sessions maintain negotiated protocol capabilities, active subscriptions, and in-progress tool calls across multiple interactions. Routing MCP traffic requires inspecting JSON-RPC message bodies, not HTTP metadata. Solo.io’s engineering team documented the practical consequence: “While you might be able to force your existing API gateway to handle basic MCP traffic, doing so means accepting significant compromises in functionality, performance, and maintainability.”
Against iPaaS (MuleSoft Anypoint, Dell Boomi, Workato): iPaaS platforms provide vast pre-built connector libraries — MuleSoft alone ships more than 1,000 — visual workflow designers, managed scaling, and enterprise governance. MCP provides none of this natively. But the convergence is striking: MuleSoft launched its MCP Connector in 2025 — the current 1.x branch documented at MuleSoft’s connector release notes added Default Request Headers in July 2025 and distributed-tracing support in August 2025 — allowing any Mule application to act as an MCP server or client and effectively turning every MuleSoft-connected system (SAP, Oracle, legacy SOAP services) into an MCP-accessible tool. Workato ships enterprise MCP support with hosted servers, OAuth, identity-aware execution, and audit logging. The pattern is clear: MCP is not replacing iPaaS but becoming the AI-native interface layer on top of existing integration infrastructure.
| Capability | Traditional middleware | MCP |
|---|---|---|
| Dynamic capability discovery | Static, design-time registration | Runtime tools/list, resources/list |
| Semantic tool descriptions | None — WSDL/OpenAPI for developers | Natural language plus JSON Schema for AI reasoning |
| Orchestration model | Human-designed rules, deterministic | AI-driven, non-deterministic |
| Transaction management | XA, 2PC, guaranteed delivery | Not supported |
| Data transformation | DataWeave, XSLT, ETL engines | Not built-in |
| Monitoring and audit | Mature consoles and dashboards | Emerging via MCP gateways |
| Auth model | API keys, mTLS, OAuth 2.0 | OAuth 2.1 with PKCE (HTTP transport) |
| Stateful sessions | Optional | Native — capabilities, subscriptions, tool-call state |
Operators who already run MuleSoft, Boomi, or Kong should not interpret MCP as a replacement project. The pragmatic architecture pairs an iPaaS or API gateway for system-to-system integration with an MCP layer — typically gateway-fronted — for agent-to-tool access. Lead-gen platforms that already invested in REST APIs and webhook infrastructure can layer MCP on top in months, not years. The cost is governance work, not re-platforming.
What this means for lead-distribution platforms
The lead-distribution platform space — boberdoo, Phonexa, LeadsPedia, ClickPoint, AquaLead, dozens more — sits at the convergence of four MCP-relevant pressures: buyers experimenting with AI procurement agents, regulators demanding granular consent audit trails, sellers consolidating onto fewer platforms with deeper integrations, and a generation of operators raised on REST APIs who now expect agentic interfaces. For a deeper comparison of these platforms see lead-distribution platforms compared: boberdoo, LeadsPedia, Phonexa.
Three categories of MCP exposure surface immediately for these platforms:
Read-only metric tools. Campaign performance, ping-post fill rate, buyer SLA status, lead disposition history, return-rate distributions. These are low-risk to expose because they do not change state. A buyer’s procurement agent can query “What is the 30-day fill rate for Florida Medicare leads in Phonexa, broken down by buyer tier?” and receive a structured answer without any platform write action. boberdoo and LeadsPedia could ship these tools in a sprint. The competitive question is which platform ships first and locks in agent-mediated buyer relationships before commodification.
Lookup and validation tools. TrustedForm certificate retrieval, Jornaya consent verification, DNC scrub status, vertical-specific eligibility rules. These are also read-only but compliance-adjacent — a buyer agent calling verify_trustedform(cert_id) through an MCP tool gets the same answer as a direct ActiveProspect API call, but with the platform’s added context (who originated the lead, which campaign, what consent language was shown). The value the platform adds is metadata, not raw access.
Write actions — gated. Releasing a held lead to a specific buyer, adjusting bid floors, pausing a campaign, accepting a return. These require careful governance. The pattern from production deployments — Block, Cloudflare, Salesforce — is to gate write actions behind explicit human approval workflows or to expose them only to internal agents under tightly controlled identity boundaries. A lead-distribution platform that lets an external buyer’s agent autonomously adjust bid floors invites both prompt-injection abuse and TCPA-violation accountability gaps.
The business model implications are non-trivial. Platforms that expose ping-post and buyer-routing logic as MCP semantic interfaces become defaults for agent-mediated procurement. Platforms that do not are routed around. This mirrors the 2010-2014 transition when ping-post became standard — sellers who refused saw fill rates decline as buyers consolidated onto auction-capable platforms. The 2026-2028 equivalent is MCP-compatible inventory.
A specific scenario clarifies the stakes. A national auto-insurance carrier deploys an internal procurement agent that queries lead-distribution platforms for inventory matching its bid criteria — Florida driver, age 25-65, current liability coverage, opted-in for SMS contact, TCPA-verified within last 24 hours. If three platforms expose this query as an MCP tool returning structured matches and one exposes only a documented REST API requiring custom client code, the agent will preferentially query the three. Over six months, the API-only platform sees a 12-15 percent fill-rate decline as the agent’s volume concentrates elsewhere. The API still works; the agent just does not use it.
For operators, the implication is that MCP exposure is now part of platform competitive positioning, not optional infrastructure. The cost of inaction is not zero.
The governance gap — what MCP doesn’t solve
When MCP functions as enterprise middleware rather than a developer tool, the security and governance implications intensify dramatically. The protocol now mandates OAuth 2.1 with PKCE for all HTTP-transported connections, with servers acting as OAuth 2.1 resource servers, mandatory token audience validation, and protected resource metadata for auto-discovery. Significant gaps remain.
The most critical unresolved threat is prompt injection through MCP tools. Invariant Labs demonstrated in May 2025 that a malicious GitHub issue containing hidden instructions could cause an AI agent to exfiltrate salary information and private project details via a public pull request — all through the legitimate GitHub MCP server. Palo Alto Networks’ Unit 42 research demonstrated multi-turn persistent prompt injection through MCP sampling, where malicious instructions persist across entire conversations. Tool poisoning attacks, where MCP tools silently mutate their definitions after installation, compound the problem. As Simon Willison warns: “We’ve known about prompt injection for more than two and a half years and we still don’t have convincing mitigations.”
For lead-gen operators, the threat surface is specific. A lead-buying agent reading inbound leads from a platform MCP server could be manipulated by a malicious lead — text in a comment field, a custom “notes” attribute, a TrustedForm metadata payload — into exfiltrating buyer pricing rules, leaking other buyers’ fill rates, or accepting a fraudulent lead. The mitigations are layered: input sanitization at the platform, output filtering at the agent, strict tool-call boundaries that prevent the agent from chaining “read lead detail” with “send email to buyer X” without explicit permission boundaries.
MCP has no built-in RBAC, ABAC, audit logging, or row-level access control. Authorization must be implemented at the server or gateway level. Audit capabilities are session-specific and designed for debugging, not compliance — insufficient for HIPAA’s 6-year retention requirements, SOC 2’s event investigation requirements, or GDPR’s processing records obligations. The emerging enterprise pattern layers MCP gateways for centralized auth, rate limiting, and audit logging, plus identity providers (Okta’s Cross-App Access, Azure AD), AI security platforms (CrowdStrike, Pillar Security), and data governance layers (Informatica, DataHub, Snowflake governance) on top of the base protocol.
The “shadow MCP” problem mirrors shadow IT: developers can install MCP servers from CLI without IT approval, creating ungoverned integration points that bypass enterprise security perimeters. Block’s approach — maintaining an internal allow-list of approved MCP servers and requiring all servers to be authored internally — represents current best practice but demands significant engineering investment that smaller lead-gen operators will struggle to match.
The TCPA-specific governance gap deserves explicit treatment. MCP transports tool definitions and data; it does not enforce consent requirements. A buyer agent calling route_lead does not know whether the lead has PEWC-compliant prior express written consent unless the platform encodes that check in the tool. This means TCPA enforcement remains the platform’s responsibility, not the protocol’s. Operators who treat MCP as an offload of compliance obligations are setting up violation exposure.
B2B SaaS and ecommerce mapping: semantic product interfaces
The lead-gen sector is not the only domain rethinking platform interfaces around MCP. B2B SaaS and ecommerce show parallel patterns that inform what lead-distribution platforms should ship.
In B2B SaaS, the dominant pattern is exposing customer-facing workflows as MCP tools. Stripe ships 23-plus tools for payment processing through its official MCP server with OAuth authentication. Salesforce offers hosted MCP servers for CRM data. GitHub provides 100-plus tools for repository management, rewritten in Go with Anthropic collaboration. The common thread: these vendors expose operations their customers’ AI agents would otherwise build custom clients to access. The vendor’s MCP server becomes a sticky integration surface — a customer that builds AI workflows against Stripe MCP tools is harder to migrate off Stripe, regardless of pricing pressure.
In ecommerce, Google’s Universal Commerce Protocol — UCP — sits as a domain-specific layer on top of MCP and A2A. Developed with Shopify, Etsy, Target, and Walmart, UCP standardizes the shopping lifecycle for AI agents — discovery, checkout, payments, post-purchase — and is transport-agnostic, working via REST, MCP, or A2A bindings. It already powers checkout in Google’s AI Mode in Search, with endorsement from Visa, Mastercard, American Express, Stripe, and 20-plus retail partners. The pattern that matters for lead-gen is the layered architecture: a domain protocol on top of MCP, not as a replacement. The same architecture suggests an “Agentic Lead Procurement Protocol” — a domain-specific layer encoding ping-post, vertical eligibility, consent verification, and waterfall logic — could emerge atop MCP within 18-24 months. Whether it comes from a trade association (LeadsCouncil) or a platform consortium (boberdoo, Phonexa, LeadsPedia jointly) determines who controls the semantic standards.
This intersects with broader work on enterprise data fragmentation and how MCP plus RAG addresses it. Lead-gen platforms sit on highly fragmented data — campaign metadata, buyer rules, vertical configurations, regulatory disclosures — that no single buyer can practically aggregate. MCP servers exposing this data with semantic descriptions let buyer agents query across platforms with consistent semantics, even when underlying schemas differ.
The semantic-product-interface idea — that a vendor’s MCP surface is a product, not a connector — explains why vendors are investing in bespoke server quality rather than auto-generating from OpenAPI. Tools without good descriptions, properly typed inputs, and behavioral annotations get worse outcomes from agents than no tools at all. Operators evaluating vendor MCP quality should look at description specificity, input validation, error messages, and changelog discipline — not just tool count.
The 12-month adoption curve and operator playbook
The next 12 months — April 2026 through April 2027 — will determine whether MCP’s governance model matures fast enough to match its adoption velocity. The protocol lacks transaction management, guaranteed delivery, built-in audit trails, and robust authorization — features traditional middleware refined over decades. Prompt injection through MCP tools remains fundamentally unsolved. The pattern from past infrastructure cycles suggests three phases.
Months 0-4 (April-August 2026): Read-only proliferation. Lead-gen platforms ship MCP servers exposing reporting metrics, lookup tools, and validation surfaces. boberdoo, Phonexa, and LeadsPedia each face pressure to be first or fast-follower. Buyer agents experiment with cross-platform queries. The platforms that ship semantic descriptions — not just OpenAPI auto-generation — see preferential agent traffic. MCP gateways (Composio, Microsoft mcp-gateway, IBM ContextForge) move from early-adopter experiments to default deployment for any platform exposing more than 10 tools.
Months 4-8 (August-December 2026): Governance hardens. Prompt-injection mitigations mature. Enterprise MCP gateway products add policy enforcement that rivals traditional API management. The first major TCPA-violation case attributed to an agent-mediated lead transaction surfaces, prompting the FCC and state AGs to issue guidance on agentic procurement. Lead-gen platforms that exposed write actions without governance face regulatory scrutiny; those that gated writes behind human approval workflows benefit.
Months 8-12 (December 2026-April 2027): Domain protocols emerge. A lead-gen-specific protocol layer — analogous to UCP for commerce — appears, either from LeadsCouncil, a platform consortium, or a vertical-specific group (auto insurance, Medicare, solar). This protocol encodes ping-post semantics, consent verification, return-rate handling, and dispute resolution as standard interfaces. Platforms participating in the standard see network effects; those holding out face buyer pressure.
The operator playbook for the next 12 months is concrete:
- Audit existing API surfaces for MCP-exposability. Read-only metric and lookup endpoints are first candidates. Documented REST APIs with stable schemas convert to MCP tools in days, not months.
- Stand up an internal MCP gateway (Composio for hosted, Microsoft mcp-gateway for self-hosted Kubernetes, IBM ContextForge for enterprise federation). Route all MCP traffic through it for auth, rate limiting, and audit.
- Implement OAuth 2.1 with PKCE for all HTTP-transported MCP connections. Use per-buyer scoped tokens — not shared API keys.
- Maintain an internal allow-list of approved external MCP servers. Mirror Block’s pattern: prefer internally-authored servers over third-party for high-trust surfaces.
- Resist exposing write actions until prompt-injection mitigations harden. When write actions ship, gate them behind explicit human-in-the-loop approval or strict identity boundaries.
- Track tool usage telemetry separately from LLM logs. Audit requirements differ — LLM logs capture conversation; tool logs capture authorized actions. SOC 2 and HIPAA care about the latter.
- Treat MCP server quality as product quality. Tool descriptions, input validation, error messages, and changelog discipline determine agent outcomes. Auto-generated servers from OpenAPI are starting points, not finished products.
- Plan for domain protocol participation. When a lead-gen-specific layer emerges atop MCP, early participants shape semantics. Late participants conform to others’ definitions.
Cross-reference: operators planning broader AI agent integration in lead workflows should also review MCP integration playbooks for CRMs, ping-post, and consent systems and the foundational explainer on MCP as universal AI data connector for protocol-level details. The browser-runtime variant — WebMCP and browser AI agents — covers the client-side equivalent that complements server-side enterprise middleware deployments.
Key Takeaways
- MCP crossed from translation layer to enterprise middleware in 16 months, evidenced by 97 million monthly SDK downloads, 10,000-plus published servers, and Linux Foundation governance under the Agentic AI Foundation since December 2025. Operators evaluating MCP as an “AI integration option” are 12 months behind the curve.
- The three-primitive design — tools, resources, prompts — separates MCP from API translation. Dynamic discovery via
tools/listand runtime capability negotiation make MCP middleware in architectural fact, not marketing label. Lead-gen platforms exposing only REST endpoints without semantic descriptions miss the layer where competitive differentiation now happens. - The agentic semantic layer is shipping in production at dbt, AtScale, Dremio, Looker, Strategy, and Bonnard. The pattern — governed metric definitions exposed via MCP, with row-level access control and business-context metadata — is the missing piece in lead-gen platforms’ agentic-commerce plans.
- MCP does not replace ESBs, API gateways, or iPaaS — it sits on top of them as the AI-native interface layer. Operators running MuleSoft, Boomi, or Kong should layer MCP, not replatform. MuleSoft’s MCP Connector (released in 2025, with ongoing 1.x updates documented in MuleSoft’s release notes) and Workato’s MCP support demonstrate the convergence pattern.
- Lead-distribution platforms — boberdoo, Phonexa, LeadsPedia — face structural pressure to expose read-only metric and lookup tools as MCP. Read-only exposure is low-risk and high-leverage. Write actions require governance maturity before exposure.
- The governance gap is real: no built-in RBAC, no audit logging that meets HIPAA or SOC 2 retention requirements, and no convincing prompt-injection mitigation. Production deployments layer MCP gateways, identity providers, and AI security platforms on top of the base protocol.
- TCPA enforcement is not transferred by MCP. Consent verification, PEWC compliance, and DNC scrubbing remain the platform’s responsibility regardless of how leads are routed. Operators treating MCP as compliance offload are setting up violation exposure.
- A domain-specific protocol layer for lead-gen — analogous to Google’s UCP for commerce — will likely emerge within 18-24 months. Early participants shape semantics around ping-post, consent, returns, and disputes. Late participants conform.
Sources
- Anthropic — Introducing the Model Context Protocol (Anthropic, 2024)
- Model Context Protocol Specification (modelcontextprotocol.io, 2025)
- Linux Foundation — Announcing the Agentic AI Foundation (Linux Foundation, 2025)
- Gartner — Innovation Insight: MCP Gateways (Gartner, 2026)
- Cloudflare — Code Mode for MCP Servers (Cloudflare, 2025)
- MuleSoft MCP Connector Release Notes — Mule 4 (Salesforce/MuleSoft, 2025)
- Solo.io — Why Existing API Gateways Fall Short for MCP (Solo.io, 2025)
- Block — Goose Open-Source AI Agent (Block, 2025)
- Invariant Labs — GitHub MCP Vulnerability Disclosure (Invariant Labs, 2025)
- Google Developers Blog — A2A: A New Era of Agent Interoperability (Google, 2025)
Frequently Asked Questions
What is the Model Context Protocol and why does it matter as enterprise middleware?
MCP is an open protocol Anthropic released in November 2024 that defines how AI agents discover and invoke tools, resources, and prompts on remote servers via JSON-RPC. It matters as middleware because it shifted from a tool-calling shim to a semantic interface layer with 97 million monthly SDK downloads, 10,000-plus published servers, and Gartner predicting 75 percent of API gateway vendors will include MCP support by 2026. The distinction matters because middleware reshapes architecture decisions around governance, discovery, and orchestration in ways a translation layer does not.
How does MCP differ from an API gateway or ESB?
API gateways handle stateless north-south traffic at the perimeter using URL paths and headers. MCP handles stateful east-west traffic between agents and tools inside the enterprise, with sessions that maintain negotiated capabilities, subscriptions, and in-progress tool calls. ESBs route messages between predetermined endpoints based on human-designed rules. MCP introduces non-deterministic orchestration where the LLM decides workflow at runtime. They sit at different layers and solve different problems.
What is the agentic semantic layer?
The agentic semantic layer is a metadata layer between AI agents and enterprise data that defines business metrics, enforces access control, and exposes governed query interfaces. Instead of an agent generating raw SQL, it calls governed metric definitions exposed via MCP. dbt, AtScale, Dremio, Looker, Strategy, and Bonnard all ship MCP servers built on this pattern. The agent never interprets column names — it queries pre-defined business semantics with row-level access controls applied automatically.
What does MCP mean for lead-distribution platforms like boberdoo and Phonexa?
Lead-distribution platforms face structural pressure to expose ping-post, routing rules, TrustedForm validation, and buyer waterfall logic as MCP-compatible semantic interfaces. Buyers running AI procurement agents want to compare lead inventory across platforms without building custom adapters per vendor. Platforms that ship MCP servers can be queried by buyer agents with tool descriptions like “price a Medicare lead in Florida with TCPA-verified consent.” Platforms that do not risk being routed around as buyers consolidate purchasing through agents that prefer MCP-compatible suppliers.
Does MCP solve TCPA compliance and consent management?
No. MCP transports tool definitions and data — it does not enforce TCPA consent capture, PEWC requirements, or DNC scrubbing on its own. Compliance must be implemented at the server or gateway level. The protocol added OAuth 2.1 with PKCE for HTTP-transported connections, but it has no built-in RBAC, ABAC, audit logging, or row-level access control. For lead-gen operators, this means TrustedForm, Jornaya, and consent platforms must continue running as enforcement layers — MCP just makes them addressable by AI agents through governed tool definitions.
What is an MCP gateway and which vendors offer them?
MCP gateways are infrastructure products that aggregate, secure, and govern multiple MCP servers behind a single control plane. Composio operates the most prominent commercial gateway with 500-plus vetted integrations, SOC 2 and ISO 27001 certification, action-level RBAC, and audit trails. Microsoft’s open-source mcp-gateway provides Kubernetes-native session-aware routing with Azure Entra ID. IBM ContextForge federates MCP, A2A, and REST/gRPC APIs with 40-plus plugins. Gartner has published a dedicated Innovation Insight: MCP Gateways report, recognizing this as a distinct infrastructure category.
How does MCP relate to A2A and UCP protocols?
MCP, A2A, and UCP form a layered agentic protocol stack. MCP handles agent-to-tool communication. Google’s A2A protocol, donated to the Linux Foundation in June 2025, handles agent-to-agent communication — how separate specialist agents discover each other, delegate tasks, and coordinate workflows. UCP — Universal Commerce Protocol, developed by Google with Shopify, Etsy, Target, and Walmart — sits on top of MCP and A2A as a domain-specific layer for shopping transactions. A planner agent might use A2A to delegate to a specialist, which then uses MCP to access tools and data.
What is the operator playbook for adopting MCP in lead-gen workflows?
Start by exposing read-only metric and lookup tools — campaign performance, ping-post fill rate, buyer SLA status, lead disposition history — through an internal MCP server gated by OAuth 2.1. Layer an MCP gateway in front for centralized auth, rate limits, and audit logs. Resist exposing write actions like “create campaign” or “release leads to buyer X” until prompt-injection mitigations and governance policies harden. Maintain an internal allow-list of approved MCP servers, mirroring Block’s pattern. Track tool usage telemetry separately from LLM logs because audit requirements differ.