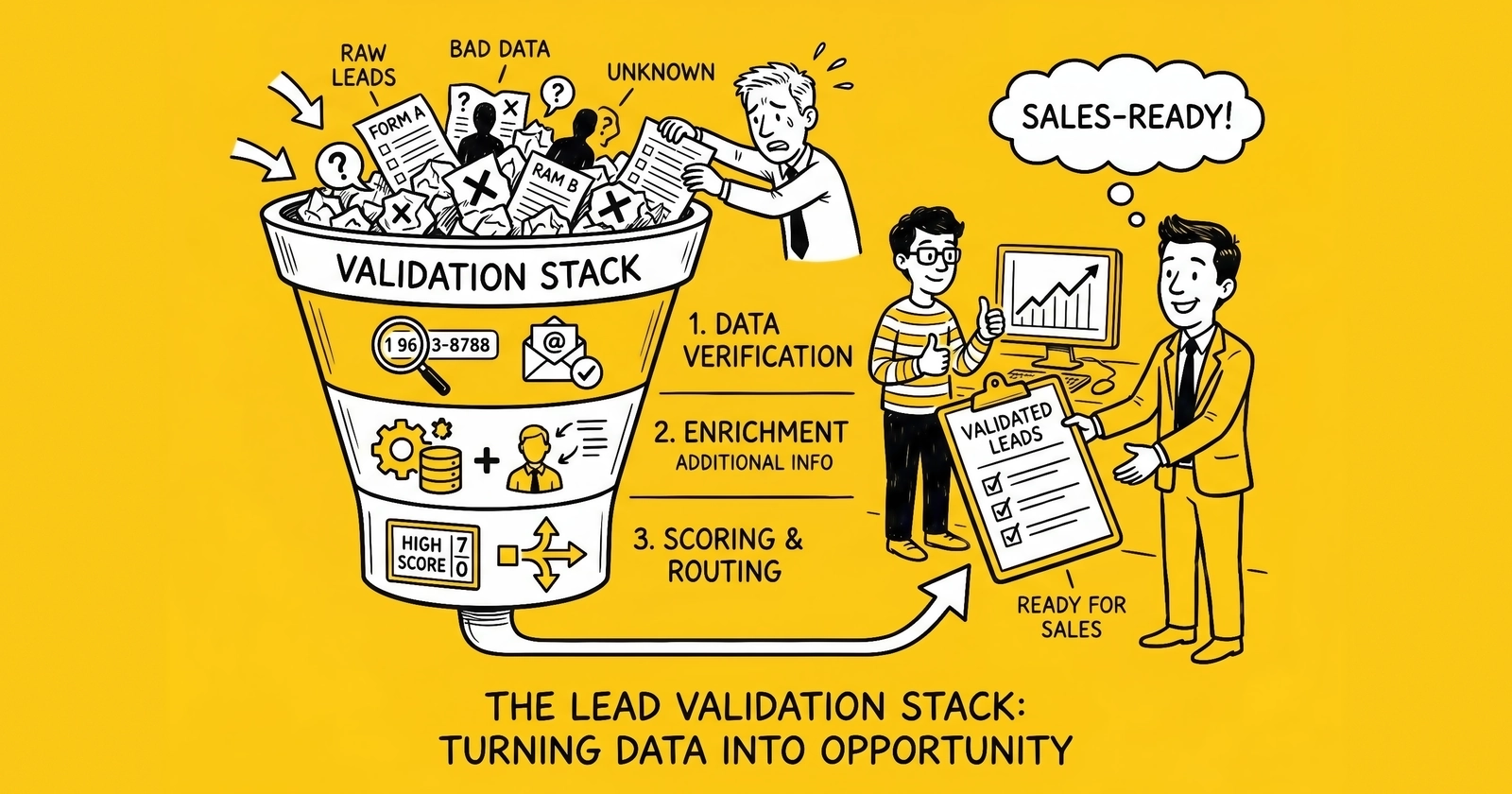
Lead validation in 2026 stopped being a checklist of vendors and became an architecture decision — orchestrated, sub-100ms, attested once, consumed by every buyer downstream.
Why fragmented validation broke
Lead generation operators spent a decade stacking validation vendors one layer at a time. A phone-validation API got bolted onto the form when the seller noticed disconnected numbers. An email-verifier got added when bounce rates crossed 8 percent. An address-standardizer arrived after the buyer rejected leads for bad ZIPs. Each layer signed its own contract, returned its own JSON shape, and ran when the operator remembered to call it.
That model collapsed in 2025 for three concrete reasons.
The first is latency. Insurance, solar, and home-services lead exchanges now run ping-post auctions where the entire ping phase — every buyer interrogated, every score returned, the auction settled — completes in under 100 milliseconds so the consumer’s form does not visibly stall. Inside that envelope, the seller has roughly 60 to 80 milliseconds to validate the lead before the auction fires. A four-vendor sequential validation chain at 80ms per call burns 320ms before the auction even starts. The lead either submits to a single buyer with no auction or the form spins for half a second and the consumer abandons. Operators running ping-post traffic discovered they could not afford sequential validation at all.
The second is multi-vector fraud. Bot farms, click-injection scripts, residential-proxy networks, and human fraud farms now defeat any single validation layer. A phone-only validator passes a real number that a fraud farm bought on a burner SIM. An email-only validator passes a freshly registered Gmail with valid SMTP. An IP-only check passes a residential-proxy exit. The site’s analysis in bot leads representing 25 percent of delivered traffic and the harder problem of human fraud farms showed that detection requires correlation across phone, email, IP, device, and behavioral signals — not any single layer.
The third is the regulatory shift. The 2025 surge in TCPA class actions — Q1 2025 alone saw 507 filings, a 112 percent year-over-year increase, and September 2025 set a single-month record of 224 — turned validation from an operational nicety into a litigation defense. Maryland’s MODPA, which began enforcement April 1, 2026, layered on a strict data-minimization rule: validation calls that pull data not strictly necessary for the consumer’s requested service became a $10,000-per-violation exposure. Operators needed validation that was both more comprehensive and more documented, executed in less time, with a clear audit trail of which checks ran and why.
The pattern that emerged — and the one this article maps in detail — is a five-layer concurrent validation stack with a TrustedForm-style attestation envelope that lets every downstream buyer consume the validation results without re-running them. Operators call it validate-once, attest-many. The vendor map underneath it has consolidated around a small set of names: Trestle, IPQS, BriteVerify, Stripe Identity, Persona, Veriff, Twilio Lookup, and the FCC’s Reassigned Numbers Database.
The five validation layers
Every modern lead validation stack maps to five layers. They run in parallel, write their results into a shared envelope, and feed both the lead-routing logic and the long-term compliance archive.
Layer 1 — Phone
The phone layer answers four questions: is the number syntactically valid, what line type is it (mobile, landline, fixed VoIP, non-fixed VoIP, toll-free), is it currently active, and has it been reassigned. Line type drives TCPA wireless determination — a number returning “mobile” or “non-fixed VoIP” is treated as wireless for prior-express-written-consent purposes, and a misclassification turns a compliant call into a $500 to $1,500 statutory violation. Active-line status filters disconnected and dormant numbers before the buyer pays. Reassignment status, when paired with the FCC Reassigned Numbers Database, unlocks the TCPA safe harbor for the first call after consent.
Vendors covering phone in 2026: Trestle Phone Validation and Phone Intelligence, Twilio Lookup v2 with the line_type_intelligence and reassigned_number packages, IPQS Phone Reputation, Ekata Phone Intelligence (Mastercard), and the FCC RND for the safe-harbor anchor. The site’s phone validation API comparison goes deeper on Twilio versus Plivo trade-offs.
Layer 2 — Email
The email layer separates syntactically valid addresses from deliverable inboxes. The four checks that matter: syntax and domain MX-record presence, mailbox existence via SMTP probe, disposable-domain detection (Mailinator, Guerrilla, the dozens of throwaways), and risk scoring based on age and breach data. Bounce rates above 5 percent damage sender reputation; rates above 10 percent get the operator’s domain blocklisted by Gmail and Outlook within weeks.
Vendors: BriteVerify (Validity), IPQS Email Verification, Trestle Email Validation, ZeroBounce, NeverBounce, Bouncer, Kickbox. BriteVerify dominates enterprise marketing automation integrations; IPQS leads when fraud signals matter more than pure deliverability. The site’s email verification services comparison walks through the deeper trade-offs.
Layer 3 — Address
The address layer standardizes input to USPS CASS or international postal formats and confirms deliverability. For service verticals — solar, roofing, HVAC, pest control — it also confirms geographic eligibility. For mortgage and insurance, it cross-checks against property records. CASS-certified output is required for bulk-mail discounts and is a quiet quality signal; non-CASS addresses correlate with bot and farm leads.
Vendors: Trestle Smart CASS, Melissa Address Verify, USPS Web Tools, SmartyStreets, Loqate, Google Address Validation API. The site’s address validation guide covers vendor differences in detail.
Layer 4 — Identity
The identity layer runs only when the vertical requires it: mortgage, financial services, healthcare-payer KYC, and some Medicare flows. The check confirms a real person matches the submitted name, date of birth, address, and government-issued document. Output ranges from a simple match score (Trestle Real Contact, Ekata Identity Check) to full document-and-selfie KYC (Stripe Identity, Persona, Veriff, Onfido, Jumio).
Pricing diverges sharply at this layer. Match-score identity runs $0.10 to $0.50 per lookup. Full document-plus-biometric KYC runs $1.50 to $3.00 per verification. Operators who do not need KYC should not buy it — the cost compounds against margin and the data collected raises MODPA exposure.
Layer 5 — Behavioral and device
The behavioral layer captures signals the consumer cannot easily fake: IP reputation, proxy and VPN detection, device fingerprint, browser anomalies, mouse-and-keystroke patterns, and form-fill timing. It runs on the lead-capture page in real time and produces a fraud score that catches what the per-field validators miss.
Vendors: TrustedForm (consent and session capture), IPQS Bot Detection, Anura, Sift, BehavioSec, BioCatch, DataDome, HUMAN, PerimeterX. The behavioral layer is the only one that detects human fraud farms — humans typing on real devices through clean residential IPs — because every other layer passes them. The detail is in the human fraud farms analysis and the broader lead fraud detection guide.
Trestle in 2026 — what it covers
Trestle’s market position is the cleanest illustration of how the validation vendor map consolidated. The corporate trail matters because operators still encounter Whitepages Pro and Ekata references in legacy contracts.
Whitepages Pro spun off from Whitepages and rebranded as Ekata Inc. in June 2019. Mastercard acquired Ekata in 2021 for $850 million, folding it into Mastercard’s identity-and-fraud product line. Trestle was founded in 2022 by former Ekata leaders who left after the Mastercard integration, and Trestle now operates as an independent identity-data API platform competing against the same Ekata products its founders built. The lineage matters for buyers evaluating both: Trestle and Ekata Pro Insight cover overlapping surface area, but Trestle is the leaner, self-service-friendly option, while Ekata-Mastercard is the enterprise-suite offering with card-network fraud signals attached.
Trestle’s 2026 product line:
Phone Validation API — line type, carrier, port history, active status. Self-service pricing from $0.015 per query at low volume, with enterprise contracts undercutting that for usage above 10,000 queries per month.
Phone Intelligence API — adds caller name (CNAM), reverse phone lookup, and identity match against the underlying Trestle identity graph.
Caller Identification API — real-time caller name and risk for inbound contact centers.
Real Contact — consolidated lead-quality score combining phone, email, and address signals with a single risk grade. Designed for ping-post insertion at sub-50ms latency.
Email Validation — syntax, domain, mailbox, disposable detection.
Address Validation / Smart CASS — USPS CASS-certified address standardization.
Identity APIs — name-and-address match scoring against the identity graph, distinct from Stripe Identity-style document KYC.
ActiveProspect’s LeadConduit ships native Trestle integration as an add-on service, which is the most common path for operators who want validation triggered inside the lead-capture flow without writing API glue. The site’s coverage of TrustedForm versus Jornaya and TrustedForm implementation describes how those integrations chain.
What Trestle does not do well: full document-plus-biometric KYC. For that, operators reach for Stripe Identity, Persona, or Veriff.
Vendor map — the 2026 stack
Six vendor categories, with the names that matter and what they actually cover:
| Layer | Vendor | Strength | Per-lookup cost (mid-volume) |
|---|---|---|---|
| Phone | Trestle Phone Validation | Line type, carrier, port history; LeadConduit-native | $0.005–$0.015 |
| Phone | Twilio Lookup v2 | Line-type intelligence, SIM-swap, SMS-pumping risk | $0.005–$0.04 by package |
| Phone | IPQS Phone Reputation | Fraud-leaning scoring, abuse history | $0.003–$0.012 |
| Phone | Ekata (Mastercard) | Enterprise-grade identity graph, card-network signals | Custom enterprise |
| Phone | FCC RND | TCPA safe-harbor anchor | $0.0025–$0.05 |
| BriteVerify (Validity) | Enterprise integrations (Salesforce, Marketo, Eloqua) | $0.008 list, lower at scale | |
| IPQS Email Verification | Fraud-leaning, disposable detection | $0.004–$0.008 | |
| Trestle Email Validation | Bundles with phone and address | $0.005–$0.010 | |
| Address | Trestle Smart CASS | USPS CASS, identity-graph linkage | $0.001–$0.005 |
| Address | Melissa Address Verify | International coverage, property data | $0.002–$0.008 |
| Address | Loqate | Strong international, GBG-owned | $0.002–$0.010 |
| Identity (match) | Trestle Real Contact | Combined phone-email-address risk grade | $0.05–$0.15 |
| Identity (match) | Ekata Identity Check | Mastercard-backed identity graph | Custom enterprise |
| Identity (KYC) | Stripe Identity | Document plus selfie, 100+ countries | $1.50 per verification, US |
| Identity (KYC) | Persona | Configurable workflows, KYB add-on | $0.50–$3.00 per verification |
| Identity (KYC) | Veriff | Document-plus-biometric, mid-market focus | $2–$6 per session |
| Behavioral | TrustedForm | Consent and session capture | Subscription, $0.05–$0.20 effective |
| Behavioral | IPQS Bot Detection | Device fingerprint, fraud score | $0.001–$0.005 |
| Behavioral | Anura | Direct-response ad-fraud focus | Custom |
| Behavioral | Sift | Account-level risk, payment-adjacent | Enterprise tier |
| Behavioral | BioCatch | Behavioral biometrics, banking heritage | Enterprise tier |
Three patterns inside the map. First, IPQS competes in three layers — phone, email, behavioral — with one bundle, which is the main reason it shows up in stacks where the operator wants a single fraud-leaning vendor rather than separate best-of-breed picks. Second, BriteVerify dominates email despite list pricing that looks high ($0.008 per query) because its Validity-platform integrations into Salesforce and Marketo make it the path of least resistance for marketing-ops teams. Third, KYC pricing ($1.50 to $6 per verification) is an order of magnitude above match-score identity, and operators who reach for Stripe Identity, Persona, or Veriff in non-KYC verticals are usually over-buying.
The validate-once, attest-many pattern
The single architectural shift that defines the 2026 stack is borrowed from how TrustedForm certificates already work for consent.
TrustedForm Certify embeds a JavaScript pixel on the lead-capture form. The pixel records the DOM, the user interactions, the timestamp, the IP, and the consent disclosure visible at the moment of submission. ActiveProspect issues a certificate URL that any downstream party can resolve to verify exactly what happened. The certificate is generated once. Every buyer in the waterfall reads it. Every buyer trusts the same cryptographic anchor. No buyer re-runs the consent capture.
Validate-once, attest-many extends that exact pattern to every other validation layer. The seller calls Trestle, BriteVerify, IPQS, the FCC RND, and Stripe Identity (when needed) once at lead capture. The results — phone line type, deliverability score, RND no-result, identity match grade, IP reputation — are sealed into a single attestation envelope keyed to the lead ID. The envelope rides with the lead through the ping-post auction. Each buyer reads the envelope and either trusts it or, for buyers with stricter rules, runs a delta validation that only adds the layers the seller did not include.
Three things make the pattern work in production:
Cryptographic signing. The envelope is signed by the seller’s key, with a Trestle or TrustedForm timestamp anchor proving the validation happened before the auction ping. Buyers can verify the signature without trusting the seller’s word.
Schema convergence. The vendors named above have largely standardized response shapes — line_type, is_valid, risk_score, is_disposable, cass_status — which makes envelope construction straightforward. The IAB Lead Generation Working Group and ActiveProspect’s certificate format both push the same direction.
Buyer co-signing. When a buyer accepts the envelope, the buyer’s own validation rules log a co-signature into the envelope’s audit trail. If a TCPA claim arises later, the audit trail shows which party validated which layer at which timestamp. That distinction matters because TCPA liability typically follows the party that placed the call, not the party that captured the lead — but co-signed validation evidence redistributes the practical defense burden.
The cost saving is direct. A waterfall with five buyers, each previously running its own three-layer validation at $0.05 per lead, spent $0.25 per lead on duplicate validation. Validate-once-attest-many runs the same three layers once at the seller and charges the buyers a small attestation-resolution fee. The site’s broader TrustedForm versus Jornaya analysis describes the same dynamic on the consent-only side; the multi-layer extension is the 2026 generalization.
Real-time vs batch — when each pencils
The validate-once-attest-many pattern is real-time by design. But not every flow needs real-time, and operators who run real-time validation across batch-loaded lists waste money.
Real-time validation belongs at the moment of lead capture — when the consumer submits the form, when a ping-post auction is about to fire, when an inbound call hits the IVR. Latency budget: 50 to 100 milliseconds. Vendors that hit this consistently: Trestle Phone Validation, Trestle Real Contact, Twilio Lookup v2, IPQS, BriteVerify real-time API, the FCC RND. The cost premium over batch is roughly 1.5x to 3x per call.
Batch validation belongs on cold lists, returned-lead reactivation files, CRM hygiene runs, and outbound-campaign list scrubs. Latency does not matter; the vendor processes 10,000 or 1,000,000 records overnight and returns scored output. Pricing drops to $0.001 to $0.004 per record at high volume. BriteVerify’s bulk pricing — $40 for 5,000, $600 for 100,000, $2,250 for 500,000 — is the canonical example.
The mistake operators make is running real-time API calls on cold-list scrubs and burning 2x to 3x the cost. The reverse mistake — running batch validation on lead-capture forms — is rarer but worse, because the latency added to the form (often 10 to 30 seconds round-trip) collapses conversion rates by 30 percent or more.
The validate-once-attest-many envelope handles both cases: batch-validated records are sealed into a batch-attestation envelope, real-time-validated records into a real-time envelope, and the audit trail records which mode applied. The site’s real-time lead validation analysis covers the buyer-side decision point in more depth.
TCPA, MODPA, and the state-law overlay
Validation in 2026 is not optional because the regulatory floor moved.
TCPA exposure remains the dominant litigation risk. Statutory damages are $500 per violation, trebled to $1,500 for willful violations. About 80 percent of TCPA cases are filed as class actions, which means a single non-compliant calling pattern across 50,000 consumers manufactures $25 million to $75 million in aggregate exposure. The 2025 filing surge — Q1 alone saw 507 class actions, a 112 percent increase, and September 2025 set a single-month record of 224 filings — pushed average settlement values past $6.6 million. Validation evidence is not a substitute for consent, but it is the second-best defense: operators who can show line-type-confirmed wireless status, RND no-result, and a TrustedForm certificate at the moment of consent collapse most class certification arguments. The site’s TCPA litigation statistics for 2025 and the TCPA compliance guide for lead generators carry the full picture.
The Reassigned Numbers Database safe harbor. The FCC’s RND query, when answered with a no-result before the call, provides explicit TCPA safe harbor for the first call after consent. The April 2025 pricing reduction (20 percent across all tiers, plus two new lower-volume tiers) made RND access viable for mid-market operators who previously skipped it. Modern stacks integrate RND into the validation envelope automatically — the no-result becomes a sealed claim downstream buyers trust. The site’s Reassigned Numbers Database deep-dive walks through the integration mechanics.
State mini-TCPA laws add a parallel exposure surface. Florida FTSA, Oklahoma TCPA, Washington, Maryland, and New York carry their own consent and timing rules. Florida’s FTSA, even after the 2023 amendment narrowed automated-system definitions, still drives meaningful filings. The validation stack has to confirm wireless status reliably enough to apply state-specific calling-window restrictions correctly. The site’s state mini-TCPA analysis covers the patchwork in detail.
Maryland MODPA is the new constraint. Effective April 1, 2026, MODPA limits sensitive-data collection to what is strictly necessary to provide the service the consumer requested. Validation calls that pull data not needed for that specific service — identity-graph enrichment for a consumer who asked only for an auto-insurance quote, for example — are now $10,000-per-violation exposure ($25,000 for repeat offenders). The practical adjustment: Maryland-eligible traffic narrows the validation envelope to checks that directly support the requested service (phone reachability, email deliverability, address CASS for service-area eligibility) and defers identity-graph enrichment until conversion. The validate-once-attest-many envelope helps document the minimization decision because the attestation lists exactly which checks ran and why.
FTC Telemarketing Sales Rule and Reg-Z apply in adjacent territory. The TSR governs outbound telemarketing fundamentals; Reg-Z applies to credit-and-mortgage lead handling. Neither is changing in 2026 in ways that reshape the validation stack, but both are part of the audit trail that validation evidence has to support.
Cost-per-saved-claim math — three vertical examples
Validation spend is justified or rejected by one calculation: cost per saved TCPA or fraud claim. Three worked examples by vertical.
Example 1 — Auto insurance, 1M leads/month
The operator runs auto-insurance lead generation at 1,000,000 leads per month with $80 average lead price. Without validation, historical TCPA exposure runs roughly 80 valid claims per month — small share of total leads, but each claim averages $1,500 in settlement value plus defense costs. Monthly exposure: $120,000 in claim payments plus an estimated $40,000 in defense legal, total $160,000.
Validation stack: Trestle Phone Validation at $0.012 per query × 1M = $12,000. BriteVerify email at $0.005 × 1M = $5,000. FCC RND at $0.01 average × 1M = $10,000. TrustedForm subscription, $4,000 per month at this volume. Total: $31,000 per month, or $0.031 per lead.
Net: $129,000 in monthly avoided claim cost against $31,000 in validation spend. Payback ratio 4.2x. Validation pencils heavily.
Example 2 — Solar leads, 200K leads/month
Solar operates at higher per-lead price ($120 average) but lower call volumes per lead (one to two contact attempts before disqualification). Historical TCPA exposure: 12 claims per month, but solar fraud (synthetic homeowner identities, address spoofing) drives a separate cost — roughly 8 percent of delivered leads return as ineligible, a $192,000 monthly loss at $120 per lead.
Validation stack: Trestle Real Contact at $0.10 per lead × 200,000 = $20,000. IPQS device fingerprint at $0.005 × 200,000 = $1,000. FCC RND at $0.02 × 200,000 = $4,000. TrustedForm at $1,500 per month. Total: $26,500, or $0.13 per lead.
Net: TCPA avoidance $14,000 plus fraud reduction (catching half the ineligible 8 percent) $96,000 = $110,000 against $26,500 in validation spend. Payback ratio 4.1x. Validation pencils. The site’s solar lead fraud analysis covers the homeownership-verification angle in detail.
Example 3 — Medicare leads, 50K leads/month
Medicare runs at lower volume but higher regulatory weight. CMS marketing rules layer on top of TCPA, and a single Compliance failure during the Annual Enrollment Period can cost an agency its CMS contracting privileges for the next plan year.
Validation stack: Trestle Phone Validation at $0.015 × 50,000 = $750. BriteVerify at $0.008 × 50,000 = $400. FCC RND at $0.025 × 50,000 = $1,250. Persona KYC for high-value enrollment confirmations, $1.50 × 10,000 (selective trigger) = $15,000. TrustedForm at $1,200. Total: $18,600, or $0.37 per lead.
Net: TCPA avoidance plus CMS contracting risk reduction is harder to quantify directly, but operators who skip the stack here are typically out of CMS contracting within two enrollment cycles. The validation cost is effectively a license fee for participation in the vertical.
The pattern across all three: validation runs $0.03 to $0.40 per lead by vertical, and the payback ratio against TCPA-and-fraud avoidance is rarely below 3x in operators with any meaningful claim history. Operators with zero claim history under-invest in validation; operators with one large class-action exposure overshoot. The middle of the curve — where most operators sit — supports validation spend of $0.05 to $0.15 per lead in non-KYC verticals and $0.20 to $0.40 in KYC-required verticals.
The 30-day stack assembly playbook
Operators standing up a validation stack from scratch can hit production in 30 days. The sequence:
Days 1 to 5 — Inventory and decisions. Catalog every existing validation call, every vendor contract, every redundant check across buyers and sellers. The audit usually surfaces 30 to 50 percent redundant spend within the first week. Pick the four anchor vendors: phone (Trestle), email (BriteVerify or IPQS), consent capture (TrustedForm), and FCC RND subscription tier matched to volume. Do not pick KYC unless the vertical demands it.
Days 6 to 10 — Schema and envelope. Define the attestation envelope structure: lead ID, validation timestamp, per-layer result, vendor ID, vendor signature, seller signature. Borrow heavily from the TrustedForm certificate format — both for legal compatibility and for buyer familiarity. Document which fields are required, which are optional, and how unknown fields degrade gracefully.
Days 11 to 18 — Real-time integration. Wire the four anchor vendors into the lead-capture flow with parallel calls. Target sub-100ms total validation time. Test with synthetic leads representing each line type, deliverability outcome, RND result, and known fraud pattern. Build the envelope assembly and signing pipeline.
Days 19 to 23 — Buyer-side resolution. Stand up the envelope-resolution endpoint for buyers. Document how buyers verify the seller signature, how they request delta validations for layers they want to add, and how co-signing works. The site’s TrustedForm implementation guide describes the analogous flow for consent certificates and is the closest existing template.
Days 24 to 28 — Production rollout. Migrate one buyer at a time. Start with the highest-volume buyer, prove the envelope round-trip, expand. Keep the legacy per-buyer validation paths active in shadow mode for two weeks to catch envelope mismatches.
Days 29 to 30 — Audit and tune. Pull two weeks of envelope logs. Confirm which layers fired, which were skipped, which buyer queries triggered delta validations. Cut underused layers. Renegotiate vendor pricing now that volume is concentrated through a single seller-side stack rather than fragmented across buyer-side calls.
The 30-day timeline assumes the operator already runs ping-post infrastructure and has at least one consent-capture vendor in place. Operators starting from manual lead delivery need an additional 30 to 60 days for the underlying ping-post and consent layers, which the site’s lead delivery methods analysis walks through in sequence.
The endpoint is a stack that costs roughly the same as the legacy fragmented model but produces sub-100ms validation, a single auditable attestation envelope, and a defensible TCPA and MODPA evidence trail. Operators who hit that endpoint typically expand the stack into more sophisticated behavioral layers (Sift, BioCatch) and KYC (Stripe Identity, Persona, Veriff) once the vertical economics support the cost. Operators who do not hit the endpoint find themselves outbid in ping-post auctions by sellers whose validated leads carry attestation envelopes the buyers prefer.
Vertical stack recommendations
Different verticals weight the layers differently. The defensible defaults:
| Vertical | Anchor phone | Anchor email | Identity layer | Behavioral | Total $ / lead |
|---|---|---|---|---|---|
| Auto / home insurance | Trestle Phone Validation + RND | BriteVerify | Skip | TrustedForm + IPQS | $0.04–$0.08 |
| Mortgage | Trestle Phone Intelligence + RND | BriteVerify | Persona or Stripe Identity | TrustedForm + IPQS | $1.80–$3.20 |
| Solar | Trestle Real Contact + RND | IPQS Email | Trestle Real Contact match | TrustedForm + IPQS device | $0.13–$0.20 |
| Legal / mass tort | Trestle Phone Intelligence + RND | BriteVerify | Skip (case-by-case) | TrustedForm + Anura | $0.06–$0.12 |
| Medicare | Trestle Phone Validation + RND | BriteVerify | Persona on selected leads | TrustedForm | $0.30–$0.50 |
| Home services | Trestle Phone Validation | IPQS Email | Skip | TrustedForm + IPQS | $0.03–$0.06 |
| Financial services / loans | Trestle Phone Intelligence + RND | BriteVerify | Stripe Identity or Persona | TrustedForm + Sift | $2.00–$4.00 |
Insurance and home services run thin stacks because TCPA exposure dominates and KYC is not required. Mortgage and financial services run heavy stacks because KYC is a regulated requirement. Solar sits in the middle because synthetic-homeowner fraud requires more device-level signals than other verticals. Medicare runs selective KYC because not every lead converts to enrollment.
Key Takeaways
- The 2026 lead validation stack is five concurrent layers — phone, email, address, identity, behavioral — running under a sub-100ms ping-post latency budget, not a chain of sequential per-vendor calls.
- Validate-once, attest-many extends the TrustedForm certificate model across every validation layer, eliminating 40 to 60 percent of duplicate validation spend in waterfalls with three or more buyers.
- Trestle (founded 2022) is the modern successor to the Whitepages Pro and Ekata identity APIs, with self-service pricing from $0.015 per phone validation query and direct ActiveProspect LeadConduit integration.
- IPQualityScore competes across phone, email, and behavioral layers with a single bundle, making it the default pick when operators want one fraud-leaning vendor instead of separate best-of-breed picks.
- BriteVerify (Validity) dominates enterprise email verification because of Salesforce, Marketo, and Eloqua integrations, with pay-as-you-go pricing starting at $40 per 5,000 verifications.
- Stripe Identity ($1.50 per verification, US), Persona ($0.50 to $3.00), and Veriff ($2 to $6) cover document-and-biometric KYC where verticals require it; non-KYC verticals should not buy them.
- The FCC Reassigned Numbers Database provides explicit TCPA safe harbor for the first call after consent, with prices reduced 20 percent across all tiers in April 2025 and integration fees as low as $0.0025 per query.
- Maryland MODPA, effective April 1, 2026, restricts validation to data strictly necessary for the consumer’s requested service, with $10,000 per-violation penalties — operators serving Maryland traffic narrow the envelope and document the minimization in the attestation.
- Cost-per-saved-claim math justifies validation spend of $0.03 to $0.40 per lead in most lead-gen verticals, with payback ratios of 3x to 5x against TCPA settlement and fraud loss avoidance.
- The 30-day stack assembly playbook — inventory, schema, real-time integration, buyer resolution, rollout, audit — is the canonical path for operators standing up validation from scratch, assuming ping-post infrastructure already exists.
Sources
- Trestle Phone Validation API (Trestle, 2026)
- Trestle Pricing (Trestle, 2026)
- IPQS Fraud Detection API Documentation (IPQualityScore, 2026)
- BriteVerify Pricing (Validity, 2026)
- Stripe Identity (Stripe, 2026)
- Persona Pricing (Persona, 2026)
- Veriff Self-Serve Plans (Veriff, 2026)
- Twilio Lookup v2 API (Twilio, 2026)
- FCC Reassigned Numbers Database (FCC, 2026)
- FCC Reduces Pricing for Reassigned Numbers Database (FCC, April 2025)
- Maryland Online Data Privacy Act analysis (Manatt, Phelps & Phillips, 2026)
- TrustedForm Certify (ActiveProspect, 2026)
Frequently Asked Questions
What is the lead validation stack?
The lead validation stack is the orchestrated set of vendors and APIs that together verify a lead is real, reachable, and legally callable before a buyer pays for it. The 2026 stack typically combines five layers: phone intelligence (Trestle, Twilio Lookup v2, IPQS), email deliverability (BriteVerify, IPQS), address standardization (Trestle Smart CASS, Melissa, USPS), identity or KYC verification (Stripe Identity, Persona, Veriff) when required, and behavioral or device signals (TrustedForm, IPQS, Sift). The five layers run in parallel under a single ping-post budget, then write their results into one envelope that downstream buyers can read without re-running checks.
What is the validate-once-attest-many pattern?
Validate-once-attest-many is the architecture pattern where each validation layer runs exactly one time at lead capture, the cryptographic results are sealed into a single attestation envelope, and downstream buyers consume the envelope rather than re-validating. It mirrors how TrustedForm certificates already work for consent and extends the same model to phone line type, email deliverability, address CASS status, RND check, and identity score. The pattern collapses redundant API spend by 40 to 60 percent in waterfalls with three or more buyers and is the only practical way to meet sub-100ms ping-post latency budgets when six or more vendors are in scope.
How does Trestle differ from Whitepages Pro and Ekata?
Whitepages Pro spun out and rebranded as Ekata in 2019, then Mastercard acquired Ekata in 2021 for $850 million. Trestle was founded in 2022 by former Ekata leaders and runs as an independent identity-data API platform. Trestle’s product line — Phone Validation, Phone Intelligence, Caller Identification, Real Contact, and Smart CASS — covers the same surface area as the legacy Whitepages Pro APIs but with self-service pricing starting at roughly $0.015 per phone validation query and volume contracts that undercut Ekata at the low end of the market. Operators evaluating both should treat Trestle as the modern, leaner equivalent and Ekata-Mastercard as the enterprise-suite alternative tied to card-network fraud signals.
How much should a validation stack cost per lead?
A full five-layer stack typically lands between $0.08 and $0.35 per lead at mid-volume tiers. Phone validation runs $0.005 to $0.015 (Trestle, Twilio Lookup), email verification $0.004 to $0.008 (BriteVerify, IPQS), address standardization $0.001 to $0.005, identity or KYC $1.50 to $3.00 when required (Stripe Identity, Persona, Veriff), and FCC RND lookups $0.0025 to $0.05 depending on subscription tier. Most lead-gen flows skip full identity checks and run only phone-plus-email-plus-RND, which keeps the cost under $0.10. Verticals that require KYC — mortgage, financial services, some Medicare flows — accept the $1 to $3 per-lead surcharge in exchange for downstream loss avoidance.
What does sub-100ms ping-post latency mean for validation?
Ping-post auctions complete the ping phase in under 100 milliseconds so the lead form does not visibly stall. Inside that 100ms budget, the seller must call every validation vendor needed to score the lead, then ping every buyer with the scored payload. Calling three sequential vendors at 80ms each blows the budget; calling six in parallel at 60ms each fits. The validate-once-attest-many pattern keeps validation inside this envelope by running all layers concurrently, caching the results once, and passing the attestation downstream so buyers do not add their own re-validation calls.
Does the Reassigned Numbers Database give TCPA safe harbor?
Yes, but only narrowly. The FCC Reassigned Numbers Database safe harbor protects callers who query the database before dialing and receive a no-result response, even if the number was actually reassigned. The protection applies to a single call only and requires three elements: prior consent from the intended recipient, a database check before the call, and a no response from the database. Pricing was reduced 20 percent across all tiers effective April 2025, with subscriptions ranging from low-volume tiers under $0.05 per query to enterprise contracts over $300,000 annually. Most lead generators integrate RND lookups directly into the validation envelope so the safe-harbor evidence rides with the lead.
How does Maryland MODPA affect validation choices?
Maryland’s Online Data Privacy Act took effect April 1, 2026 and limits sensitive-data collection to what is strictly necessary for the consumer’s requested service. Validation layers that pull data not needed for the specific product the consumer asked for now create regulatory exposure, with penalties of $10,000 per violation and $25,000 for repeat offenders. The practical effect is that operators serving Maryland traffic narrow their stack to validation calls that directly support the requested service — phone reachability, address CASS for service eligibility, email deliverability — and defer enrichment-style identity-graph queries until the consumer is converted. The validate-once-attest-many envelope helps document the minimization decision because the attestation lists exactly which checks ran.
What is the right starting stack for a new operator?
A new operator running insurance, solar, or home-services traffic at $50 to $500 cost per lead should start with four layers: TrustedForm Certify for consent capture, Trestle Phone Validation for line-type and reachability, BriteVerify or IPQS for email deliverability, and an FCC Reassigned Numbers Database subscription scaled to volume. That stack runs about $0.04 to $0.08 per lead at $50K-per-month spend and covers the highest-frequency TCPA and quality risks. Identity verification (Stripe Identity, Persona) is added only when the vertical requires KYC. Behavioral and device signals (IPQS device fingerprint, Sift) are added once fraud rates exceed 2 percent of delivered leads.